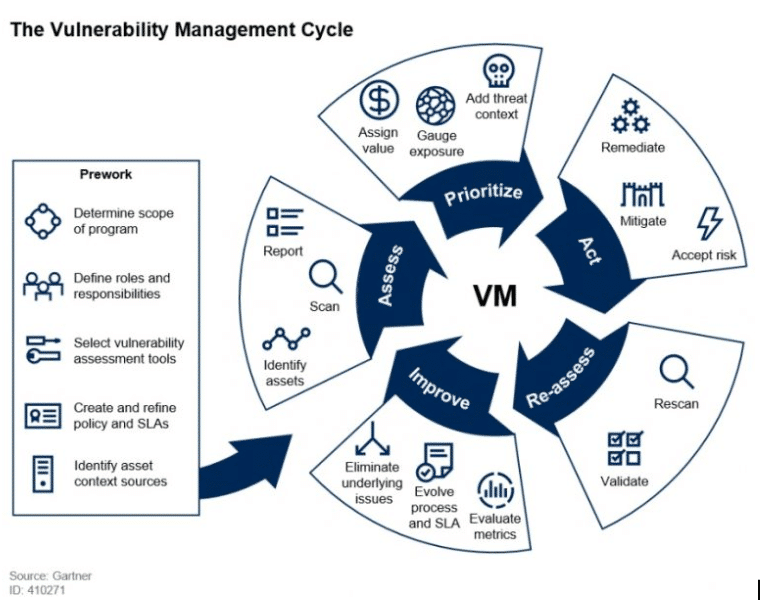
Figure 6 from Implementing a vulnerability management process GIAC ( GSEC ) Gold Certification | Semantic Scholar
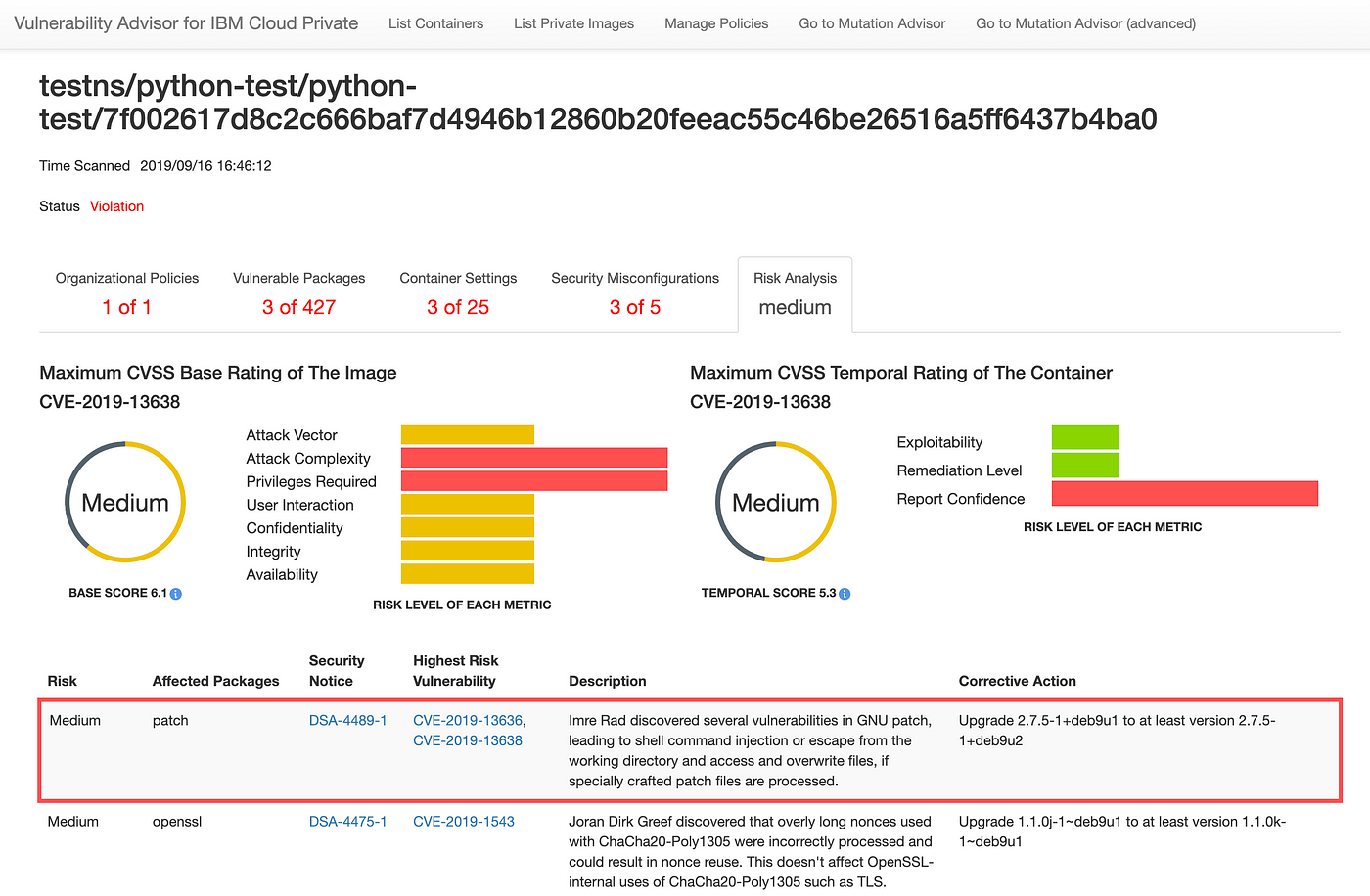
Assessing security risk of your containers with Vulnerability Advisor | by Yuji Watanabe | IBM Cloud | Medium
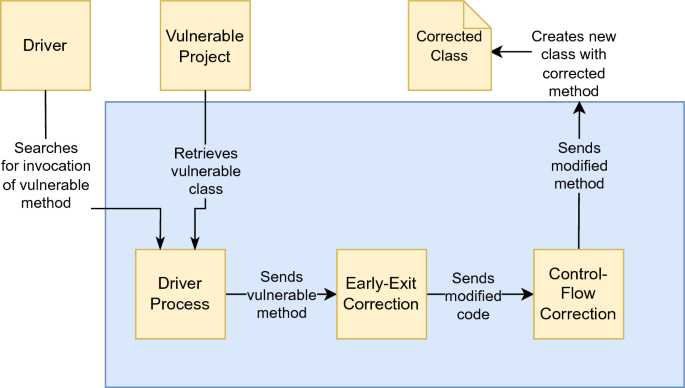
DifFuzzAR: automatic repair of timing side-channel vulnerabilities via refactoring | Automated Software Engineering
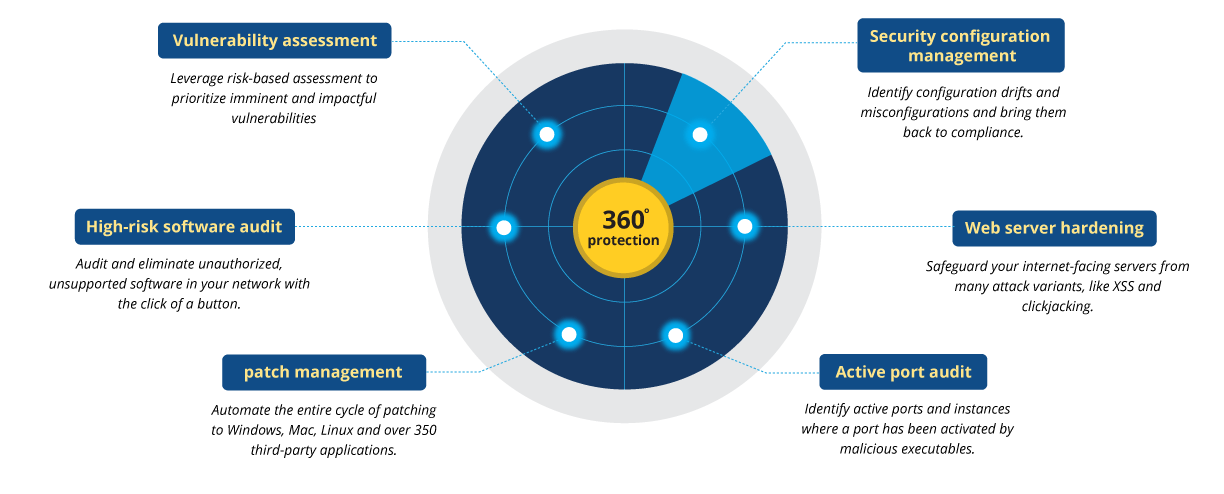
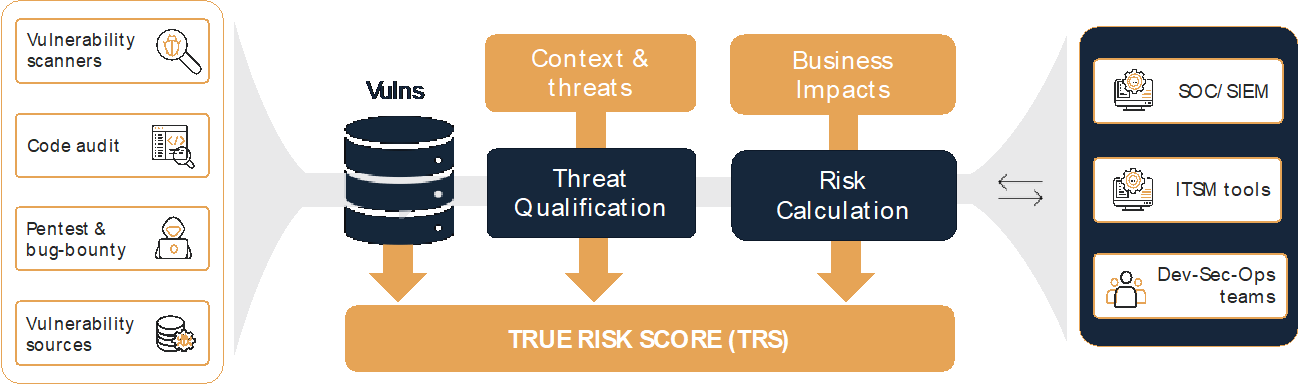
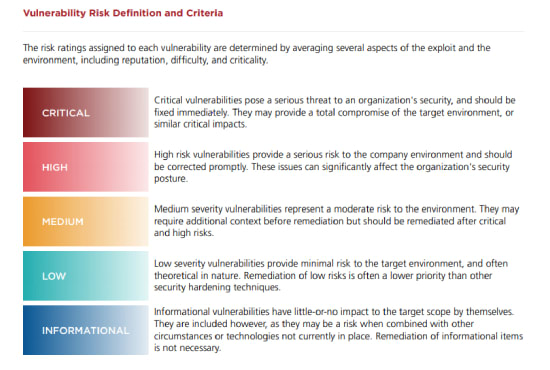
Définition de la gestion des vulnérabilités | Processus de gestion des vulnérabilités - ManageEngine Vulnerability Manager Plus

Fixing a security vulnerability in the system. Cyber security and corporate data protection. Error correction. Hacker attack. Malfunction, breakdown, out of order. Requiring a replacement. Stock Photo | Adobe Stock








![Hikvision, HWG Deceive FCC About New Critical Vulnerability [Update: Hikvision Issues Correction] Hikvision, HWG Deceive FCC About New Critical Vulnerability [Update: Hikvision Issues Correction]](https://s.ipvm.com/uploads/embedded_image/dc2924c53291893666e336b8f2a820f913a59d9f396e0468ce9f1f0a3250306f/4fec498e-fe4a-4350-a53a-3ec6e029c335.webp)